Table of Contents
Cybersecurity refers to the practice of preventing, protecting, and defending networks, devices, and electronic systems from malicious threats or cyberattacks. Normally, these digital attacks are designed with the intent of accessing, stealing, or destroying important data in order to disrupt normal business operations and gain control of sensitive information. In some extreme cases, cyberattacks are also used as a means of extorting money from users.
Therefore, cybersecurity is critical for any organization. Government, medical, corporate, and financial organizations all collect and deal with unprecedented amounts of information on a daily basis. This data is usually stored online, on company computers, or on other electronic devices. The data typically comprises highly sensitive and private information that can lead to severe consequences if leaked, deleted, or exposed. Moreover, it can put everyone at risk, from your employees to your clients.
Protection against the threat of cyberattacks should be a priority for all organizations. Businesses are becoming increasingly aware of this evolving danger and are orienting themselves to best protect their organization, employees, and other stakeholders from any kind of security breaches and cyberattacks. Through continuously updating their networks, providing their employees with risk management training, and implementing cybersecurity tools, both small startups and established businesses are finding ways to better equip themselves against cyberattacks.
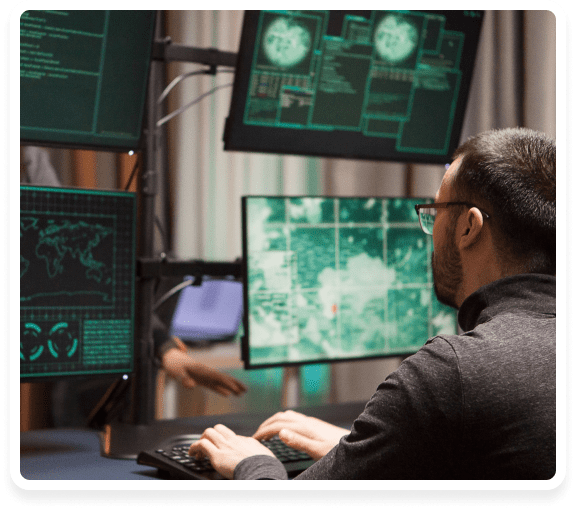
Cyberattacks are highly dynamic and a continuously evolving danger for businesses. Attackers continue to innovate and find new loopholes that they can aggressively exploit. And while antivirus software in combination with frequent updates of your network system is a good defense, cybercrime has become far more sophisticated for these measures to be enough in the current environment. Professional hackers use diverse strategies and opportunities via phishing attempts as a means of breaking through an organization’s defenses.
Poor cybersecurity can put your entire organization at risk. Financial losses are probably the most obvious consequence of a cyberattack. Professional hackers are capable of initiating fraudulent transactions and taking over your money through unauthorized transfers once they have access to your system. Your entire company productivity comes to a halt as soon as you experience a cyberattack and normal businesses operations are disrupted or put on hold while the IT staff resolves the issue.
Additionally, in the aftermath of a cyberattack, your company’s reputation can suffer tremendously. In fact, even minor security breaches can cause your clients to doubt your ability to protect their information. Investors and other stakeholders, directly or indirectly involved in your business, can become skeptical as a result of a cyberattack.
Ultimately, a lack of trust on the part of the investors, coupled with lost productivity, a pause in normal business operations, and severe financial losses, can force your organization to close.
Benefits of Good Cybersecurity
Making sure your business has good cybersecurity can have several benefits. With good cybersecurity, your business can enjoy the most comprehensive digital protection from diverse threats including, but not limited to:
- Malware programs (Trojan horses, worms, etc. that can cause severe damage to your computer and network system)
- Spyware (cyber-infection that secretly spies on all your computer activities)
- Adware (a type of virus that disrupts your computer activity by bombarding you with random advertisements)
- Ransomware (a type of virus that infects your computer system and denies access until a ransom is paid)
- Phishing (cybercrime that relies on email, telephone call, or text messages to cause damage)
Cybersecurity vs. Computer Security vs. IT Security
Although the terms cybersecurity, computer security, and IT security are oftentimes used interchangeably, they mean very different things.
Computer security refers to the protection/ security of a single computer. Essentially, the term computer security refers to the protection and defense of the software and hardware of a standalone computer. This protection can be in diverse forms, such as keeping the computer software up-to-date, using anti-malware programs, and keeping the device properly patched.
In contrast, IT security refers to the protection of data and company information.
Cybersecurity, on the other hand, refers to the protection as well as the security of all networks, systems, devices (mobiles, computers, laptops, company printers, etc) as well as the intercommunication of all of these components. To ensure your business is secure from any outside threats, you need to implement proper cyber, computer, and IT security protocols.
Cybersecurity in the Age of COVID-19
With the COVID-19 pandemic, hackers have found a new way to infiltrate and breach company systems. Professional hackers jump for opportunities like the one created by the pandemic. They are now fooling companies by sending phishing emails, finding vulnerabilities, and installing malware on company systems.
In the first quarter of 2020 alone, there have been an estimated 907K spam messages related to COVID-19 that have emerged. The time period between February and March saw a 220x increase in spam, with 260% increase in malicious URLs, which were found to be the key tool used to fool users.
How Attackers Are Exploiting the Pandemic
Phishing Email
A dramatic surge in phishing email and texts has been observed ever since the COVID-19 pandemic. Hackers all across the globe are aware that people are vulnerable right now and that they are desperate for more information on the novel coronavirus and how to protect themselves from it. They are using this subject matter to send out phishing emails containing content, URLs, and attachments claiming to have information related to COVID-19. In doing this, they are exploiting the global panic around the pandemic and using it to fool people and ultimately put them at risk by stealing their personal information and even their money in some cases.

Cyberattackers are also using bad domains and phishing websites as a means to fool people and carry out fraudulent activities. Most of these websites contain information about COVID-19 as a means of alluring people. In fact, according to statistics by Google, there has been a 350% rise in phishing websites ever since the pandemic began.
Insecure Endpoints
With more and more companies allowing employees to work from home on their personal laptops and devices and connecting to unsecured Wi-Fi, the threat to the central network security perimeter of organizations has increased. Hackers are using this opportunity and exploiting insecure endpoints as a means of gaining access to company networks easily. Securing endpoints is highly crucial because it could put your money and other resources at risk.
Amidst the pandemic, the reliance of businesses on internet technologies has increased tremendously. With companies using emails to contact employees and teams relying on conference-calling apps like Zoom to collaborate, there is an even greater need for cybersecurity and frequent patch up.
In fact, hackers in Iran have already started exploiting this loophole to their advantage. They are hacking VPN and planting backdoors in companies around the globe. Moreover, additional data shows that several Microsoft credentials have been stolen ever since the pandemic began with 4+ million Mac webcams being exposed.
Cybersecurity Stats
In 2019 alone, at least 90% of businesses organizations were the victim of targeted phishing attacks, according to a report by ProofPoint. Interestingly enough, the report also revealed that most employees do not have the sufficient training to employ basic security measures to prevent these attacks from happening.

Perhaps the most alarming statistic was revealed in a study conducted at the University of Maryland that reported that there is a hacker attack every 39 seconds which affects 1 in 3 Americans almost every year. Most of these attacks are successful because most users have unsecure usernames and weak passwords. It has been found that almost 93% of security breaches occur as a direct result of human error.
These statistics are especially alarming for businesses because a lack of proper cybersecurity measures in place can end up leading to devastating consequences. Especially, because according to statistics, nearly 43% of cyberattacks are found to target small businesses. And it is reported that most companies take a minimum of at least 6 months to detect the attack.
What Are Common Cybersecurity Threats?
The most common cybersecurity threats include:
- Computer Viruses: This is a type of malicious code or program written in order to disrupt normal computer operations. It transfers from host to host and makes copies of itself, very much like a flu virus.
- Hacker Attacks: These are attacks carried out by professional hackers who find loopholes and security weaknesses in a computer system or a network and exploit those to their advantage.
- Phishing: This form of attack relies on deception whereby the victim is tricked into trusting the attacker. Usually, this is done via spam emails containing URLs and attachments that are designed to infiltrate the system. Phishing attacks normally target sensitive information such as credit card numbers, usernames and passwords, etc.
- Spyware: This is a type of malware that infiltrates your computer, without the host realizing it, and steals information and spies on your computer and internet activity.
- Malware: Any harmful software or malicious program designed to damage your computer or network.
- Ransomware: A malicious software that takes control of your computer and denies access until or unless a ransom is paid to the attacker.
- Hidden Background Programs: These malicious programs occur in the form of spyware or adware and usually infiltrate the computer system via the internet without the user’s knowledge. These programs are usually hidden and not easily detectable without professional IT help.
- Unpatched Security Vulnerabilities: Your computers run on software. Vendors frequently offer new software updates in order to resolve any issues or bug fixes in the existing versions. Unpatched software can provide an opportunity for attackers to hack into your computer or system and cause damage. An unpatched system is a vulnerable system and a massive threat to your organization’s security.
- Denial of Service (DoS): This type of attack is used as a means of making a computer or other system unavailable to the user. Usually, DoS attacks are executed by flooding the system with information thereby leading to a crash.
- SQL Injection Attack: The attacker uses a malicious SQL code in order to attack a computer or a system. This type of attack is primarily used to gain access to sensitive information. Attackers may steal usernames, passwords, bank details, etc.
- Man in the Middle Attack (MitM): This type of attack occurs in a situation where two parties are involved in direct communication with each other. An attacker might infiltrate this communication and deceive the parties into believing that they are in direct communication, where in reality they are not. It is sort of like eavesdropping, only in this case the stakes are much higher as sensitive information or company secrets can end up in the wrong hands.
- Zero-Day Attacks: An attacker uses a weakness in the software to their advantage the same day as it becomes apparent. They carry out the attack before a fix or update becomes available.
Social Engineering
As mentioned earlier, the majority of the statistics related to cybersecurity suggest that most cyberattacks occur as a result of human error. Social engineering refers to a set of malicious strategies used by an attacker to manipulate a victim into revealing information or taking an action that could cause serious damage.
Social engineering technique relies on the use of human interaction whereby the attacker first studies the victim and figures out the weak points. The attacker then exploits these weak areas to emotionally manipulate the victim into trusting them. Eventually, this leads to the victim trusting the attacker and revealing sensitive or confidential information.
Hackers

Malware
Malware refers to any malicious software that infiltrates your computer and causes damage. These software are written with the intent of stealing information or generally causing severe damage to the device in use. Businesses can suffer significantly from malware attacks since it allows attackers to steal, delete, or use confidential business information as a means of demanding ransom.
Phishing
Phishing is another form of cyberattack that relies on spam emails and fraudulent attempts on the part of the hacker to obtain access to a user’s private information such as usernames, passwords, and other sensitive personal information, like credit card numbers. Companies can suffer tremendously from these attacks. Attackers can not only steal data and private information, but they can put the reputation of the company in jeopardy as well. Most attackers also use this method as a means of stealing money from business organizations.
Ransomware
This is a type of malware that takes control of a computer, data, or system and denies access to it until a ransom is paid to the attacker. Phishing email and malicious websites are common entry points of ransomware. Both small and large organizations can suffer tremendously as a result of ransomware attacks and up losing crucial data as well as money in the process. Ransomware attacks are so common that at least one company is attacked every 14 seconds. Moreover, stats suggest that at least 55% of small businesses end up paying the ransom. The current projected damages caused as a result of ransomware are projected to be around $20 billion by 2021.
The Dark Web
The dark web is a part of the internet that is normally inaccessible via traditional search-engines. It usually requires a very specific kind of software configuration or network in order to access it. Since it is essentially hidden, the dark web is used as the basis for carrying out several kinds of criminal activities. Attackers sell company information and personal information on the Dark Web, similar to how you would sell products on Etsy or Ebay. It’s a marketplace for selling stolen information and credentials, among several other criminal activities.
How You Can Protect Your Business
The majority of statistics related to cyberattacks suggest that most of these attacks are caused by human error. A simple way to protect your business is to have IT professionals implement cybersecurity measures on your behalf. Be sure to limit access to sensitive information by preventing employees from accessing it directly. Make sure your software and operating systems are patched up properly. Update your system and install proper firewalls and antivirus software.